- Messages
- 17,471
- Reactions
- 36,483
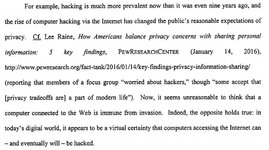
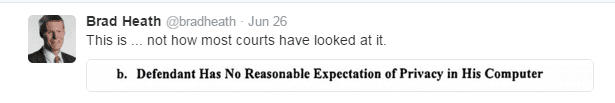
It is a scary ruling -

Federal court: Computers connected to the internet aren't private, have no 4th Am. protection. Expect to be hacked.

So, that probably includes your phone - it is connected to the internet.

Here is the court's ruling:
18917316433 (https://www.documentcloud.org/documents/2911707-18917316433.html)
The defendant is not cute & cuddly - he is a disgusting piece of bubblegum. But his rights are my rights and need to be defended. (sorry there is a word I am searching for and not finding... )
EFF weighs in:
https://www.eff.org/files/2016/06/23/matish_suppression_edva.pdf
Others:
Court Rules the FBI Does Not Need a Warrant to Hack a Computer (https://motherboard.vice.com/read/court-rules-the-fbi-does-not-need-a-warrant-to-hack-a-computer)
FBI: Exploit that revealed Tor-enabled child porn users wasn't malware (http://arstechnica.com/tech-policy/2016/06/fbi-exploit-that-revealed-tor-enabled-child-porn-users-wasnt-malware/)
http://courtswv.gov/supreme-court/calendar/2007/briefs/sept07/33295Appellee.pdf
Does this mean that if a LEO hacks your device, it could have been hacked, and therefore you don't get protection? How about if a LEO can open your safe, it could have been opened and there for you don't get protections?

Federal court: Computers connected to the internet aren't private, have no 4th Am. protection. Expect to be hacked.
So, that probably includes your phone - it is connected to the internet.
Here is the court's ruling:
18917316433 (https://www.documentcloud.org/documents/2911707-18917316433.html)
The defendant is not cute & cuddly - he is a disgusting piece of bubblegum. But his rights are my rights and need to be defended. (sorry there is a word I am searching for and not finding... )
EFF weighs in:
https://www.eff.org/files/2016/06/23/matish_suppression_edva.pdf
Others:
Court Rules the FBI Does Not Need a Warrant to Hack a Computer (https://motherboard.vice.com/read/court-rules-the-fbi-does-not-need-a-warrant-to-hack-a-computer)
FBI: Exploit that revealed Tor-enabled child porn users wasn't malware (http://arstechnica.com/tech-policy/2016/06/fbi-exploit-that-revealed-tor-enabled-child-porn-users-wasnt-malware/)
http://courtswv.gov/supreme-court/calendar/2007/briefs/sept07/33295Appellee.pdf
Does this mean that if a LEO hacks your device, it could have been hacked, and therefore you don't get protection? How about if a LEO can open your safe, it could have been opened and there for you don't get protections?